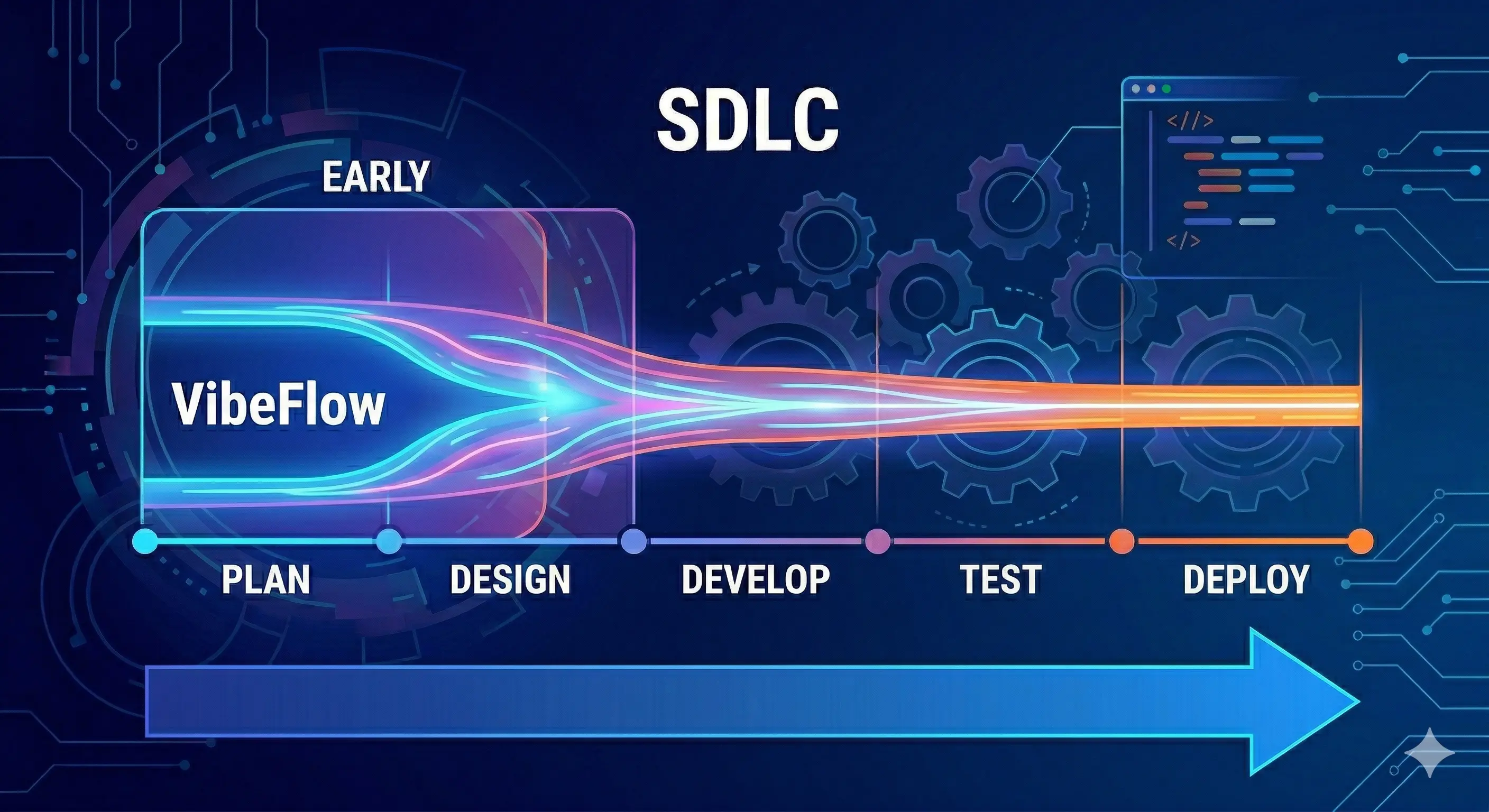
Vibecoding Shift-Left SDLC: Making VibeFlow Real for Teams
Shift-left means catching problems earlier — in design, not production; in code review, not incident response. Vibecoding makes shift-left possible at a new level of granularity. VibeFlow is the governance layer that enforces it.
“Shift left” has been a software engineering mantra for over a decade. Move testing earlier. Catch security issues in code review, not in production. Find bugs when they cost $1 to fix, not $10,000. The concept is correct, the research is clear — IBM’s Systems Science Institute found that defects caught in production cost 15× more to fix than defects caught in design.
The implementation has always lagged the principle.
Traditional shift-left initiatives face a consistent obstacle: the people doing the work (developers) are already at capacity. Adding more quality gates, more security scans, more review checkpoints means asking developers to do more with no increase in time or capacity.
Vibecoding changes this equation. AI agents don’t burn out. They don’t skip tests when under deadline pressure. They don’t defer security review because the sprint is ending. Vibecoding makes thoroughgoing shift-left practices operationally feasible in a way they haven’t been before — but only if the infrastructure exists to enforce them. That’s what VibeFlow provides.
[IMAGE: Traditional SDLC vs shift-left SDLC vs vibecoding shift-left — defect detection cost curve]
What Shift-Left Actually Means
Shift-left is the practice of moving quality, security, and validation activities earlier in the development process — closer to the point where decisions are made, rather than the point where code reaches production.
The original formulation comes from Larry Smith’s 2001 paper on testing in agile development, and was formalized in concepts like DevSecOps (integrating security into DevOps pipelines) and test-driven development.
In practice, shift-left covers several distinct practices:
Requirements validation: Catching ambiguous or contradictory requirements before implementation begins, not after a developer has spent a week on the wrong feature.
Test-first development: Writing tests before writing implementation code, so the behavior specification exists independently of the implementation.
Security by design: Making security considerations part of the design phase, not a final scan before release.
Automated quality gates: Running linting, type checking, and test suites on every commit, not just before releases.
Continuous integration: Integrating code frequently so conflicts and integration failures surface in hours, not in final-week merge hell.
Each of these is well-established. The challenge has always been that they add work to already-overloaded development processes.
How Vibecoding Enables Shift-Left
Vibecoding AI agents can be directed to follow shift-left practices without the cognitive overhead that makes those practices hard to sustain for humans under pressure.
Tests Written Alongside Code, Not After
A vibecoding agent directed to implement a feature will write tests when instructed to — and will write them consistently, without the temptation to skip them when deadline pressure arrives. The agent follows the specification it was given.
More importantly, agents can be given a test-first workflow as a standing instruction:
Task specification template:
1. Write a failing test that validates: [acceptance criteria]
2. Implement until the test passes
3. Refactor without changing test behavior
4. Run the full suite before committingWhen this workflow is encoded in the task specification — enforced by the system rather than left to individual developer discipline — it executes on every task, not on the ones where a developer remembered.
This is the core shift-left mechanism: moving the test from “written after, when there’s time” to “written first, always.”
[IMAGE: Test-first workflow enforced through task specification — failing test → implementation → green → commit]
Security Review at Commit Time, Not Release Time
Traditional security review happens late — a SAST scan in the CI pipeline at PR time, or a penetration test before a major release. Both are better than nothing. Neither is as good as reviewing security implications before the implementation is written.
Vibecoding agents can be given standing security constraints that apply to every implementation:
- “Do not construct SQL queries via string interpolation — use parameterized queries”
- “Validate and sanitize all user-supplied input before processing”
- “Do not write secrets, credentials, or API keys to files”
- “Apply authentication checks before any data access”
When these constraints are in the agent’s task specification, they’re applied during implementation — not discovered during review and handed back for rework.
This is a qualitative shift. The cost of a security fix applied during implementation is near-zero (the agent writes the secure version from the start). The cost of a security fix discovered during PR review is rework. The cost of a security fix discovered after deployment is remediation under pressure.
Requirement Clarification Before Implementation
One of the most expensive defect categories is misunderstood requirements — features built correctly to the wrong specification. In traditional development, this is caught in UAT or in production. With vibecoding, the same risk exists: an agent will implement exactly what the task says, including misinterpretations.
Shift-left means surfacing this ambiguity before implementation. VibeFlow’s agent protocol includes a mechanism for this: when an agent encounters genuinely ambiguous requirements, it creates a prompt_user event rather than guessing. The developer sees the question in the VibeFlow chat UI, answers it, and implementation proceeds from a clarified specification.
This is shift-left applied to requirements: the ambiguity surfaces in the planning phase, not the QA phase.
The VibeFlow Pipeline: Built-In Quality Gates
VibeFlow formalizes the shift-left principle into a mandatory pipeline for every work item — todo or issue — regardless of how it was created. The pipeline has five states:
planning → ready_to_implement → implementing → done → [security review] → [QA verification]This is not a suggestion. It is the enforced workflow. An agent cannot skip from implementing to done without completing the required fields (commit hash, lines changed). A completed item cannot be considered shippable until it passes both security review and QA verification.

Planning Gate: No Implementation Without a Work Item
The planning gate enforces the most fundamental shift-left principle: no code gets written without an explicit, tracked specification.
In traditional vibecoding workflows, a developer can prompt an agent to “quickly fix that bug” directly in a chat interface. The fix gets written, committed, shipped — with no record of what was changed or why, no review, no test verification.
VibeFlow’s developer agent protocol makes this explicit: before any file is modified, a work item must exist. Ad-hoc requests from the user are classified into either a todo (feature work) or an issue (bug/defect), created in the system, and transitioned through the pipeline. The classification happens at the moment the request arrives, before any implementation begins.
This enforces the shift-left principle that all work should be planned and specified before implementation — not as bureaucracy, but as the mechanism that makes downstream quality gates possible.
Security Review Gate: Mandatory After Every Implementation
Every item that transitions to done enters the security review queue. The security review gate (security_reviewed: false → true) must be cleared before the item is considered shippable.
In VibeFlow’s multi-agent architecture, a dedicated security agent processes items in the security review queue. The security agent:
- Reads the implementation diff for the completed item
- Checks for characteristic vulnerability patterns (injection, authentication bypass, secret exposure, insecure defaults)
- Either marks the item as security-reviewed (clean) or creates a linked security fix issue
The security fix issue is tracked as a separate work item that must itself complete the full pipeline before the original item is considered fully cleared.
This is shift-left security enforcement: every change, regardless of how small, receives a security review before it is considered done. Not as an annual audit. Not as a pre-release scan. After every commit.
QA Verification Gate: Behavior Verified Against Specification
The QA gate (qa_verified: false → true) is the final gate before an item is fully complete. In a multi-agent deployment, a dedicated QA agent processes items that have passed security review.
The QA agent’s job is to verify that the implementation satisfies the acceptance criteria in the original specification. This is not re-running unit tests — the implementation agent already ran those. This is independent behavioral verification: reading the specification, reading the implementation, reading the test output, and confirming that the implementation does what the specification required.
When QA finds a discrepancy, it rejects the item with specific feedback. The item returns to in_review and the implementation agent fixes only the identified issues — not a full re-implementation.
This is shift-left QA: verification happens immediately after implementation, by an independent reviewer, against a written specification. The cost of a QA rejection at this stage is one iteration of targeted fixes. The cost of a QA failure in production is incident response.
The Shift-Left Cost Curve Under VibeFlow
The IBM research finding — that production defects cost 15× more than design-phase defects — is based on human-speed development cycles. Under VibeFlow’s agent pipeline, the cost curve is compressed further:
[IMAGE: Defect cost curve comparison — traditional SDLC vs VibeFlow pipeline]
| Defect found at | Traditional SDLC cost | VibeFlow pipeline cost |
|---|---|---|
| Requirements ambiguity | Developer rework after implementation | prompt_user clarification before implementation |
| Implementation error | PR review rework | QA rejection → targeted fix (same session) |
| Security issue | Security scan → rework → re-review | Security review → linked fix item (next work cycle) |
| Production bug | Incident response, hotfix, post-mortem | Prevented by prior gates |
The pipeline doesn’t eliminate all defects — but it catches them as early as possible at agent velocity, with structured remediation paths at each gate.
Concrete Benefits: What Teams Measure
Teams operating VibeFlow-governed vibecoding pipelines report measurable outcomes across several dimensions:
Reduced rework rate: When requirements are clarified before implementation (via prompt_user gates) and QA verification happens immediately after implementation, the rate of “implement, review, reject, re-implement” cycles drops significantly. The work item transitions forward, not backward.
Faster feedback on security issues: Security issues surfaced after security review are caught within hours of implementation, by the same agent that has the implementation context fresh. Compare to traditional security audits conducted weeks or months later by reviewers who need to reconstruct intent from code.
Consistent quality across team members: In human-only development, quality varies significantly by developer — experience, current focus level, deadline pressure. Agent pipelines execute the same quality process for every work item, regardless of who created the task or when.
Audit trail completeness: Every work item in VibeFlow has a complete record: the original specification, implementation logs (with diffs), security review notes, QA verification notes, and the git commit hash. This audit trail exists by construction — it is a byproduct of the pipeline, not additional documentation work.
Transitioning from Traditional SDLC
Teams adopting VibeFlow-governed vibecoding don’t need to change their entire development process on day one. The transition typically happens in phases:
Phase 1: Instrument the work. Start using VibeFlow to track all development work items. Get visibility into what’s being built, by whom, with what rationale. This is low-friction — developers continue working as before, but every task flows through the system.
Phase 2: Enforce the planning gate. No implementation begins without a tracked work item. This is the highest-leverage shift-left intervention — it ensures specification exists before code is written.
Phase 3: Activate quality gates. Enable the security review and QA verification stages. Initially, these can be lightweight — a quick automated scan and a brief specification check. Over time, deepen the review criteria as the team learns what the agents miss.
Phase 4: Multi-agent pipeline. Deploy dedicated security and QA agents that process their respective queues autonomously. At this phase, the full shift-left pipeline runs with minimal human intervention — human time is reserved for judgment calls the agents escalate, not routine verification.
The Underlying Principle
Shift-left has always been correct as a software engineering principle. The constraint has been human capacity. When quality gates require human attention at every stage, teams have to choose between velocity and thoroughness.
Vibecoding removes that constraint. AI agents can apply shift-left practices on every change, consistently, without capacity limits. VibeFlow provides the workflow infrastructure that enforces those practices and makes their application auditable.
The result is a development process where quality isn’t something added at the end — it’s built into the pipeline from the moment a task is created to the moment it’s shipped.
Further Reading
- What is Shift-Left Testing? — IBM overview of shift-left principles and the defect cost research
- DevSecOps: Integrating Security into the Development Lifecycle — foundational DevSecOps principles
- Vibecoding and What It Means for the SDLC in Teams — companion article on full SDLC impact
- The Hidden Risks of Vibecoding — enterprise governance risks
- VibeFlow Product — the AI development governance platform
- From Vibes to Verifiable: The New Standard for AI Production Readiness
Written by
AXIOM Team